There is a big difference between adopting technology and accumulating technology. The subject of reviewing application permissions clearly shows this boundary: when there is a method, the tool helps; when there is permanent improvisation, it becomes another source of distraction. For people who have installed many apps over time, the safest path is to start with actual use, test slowly and only keep what improves their routine.
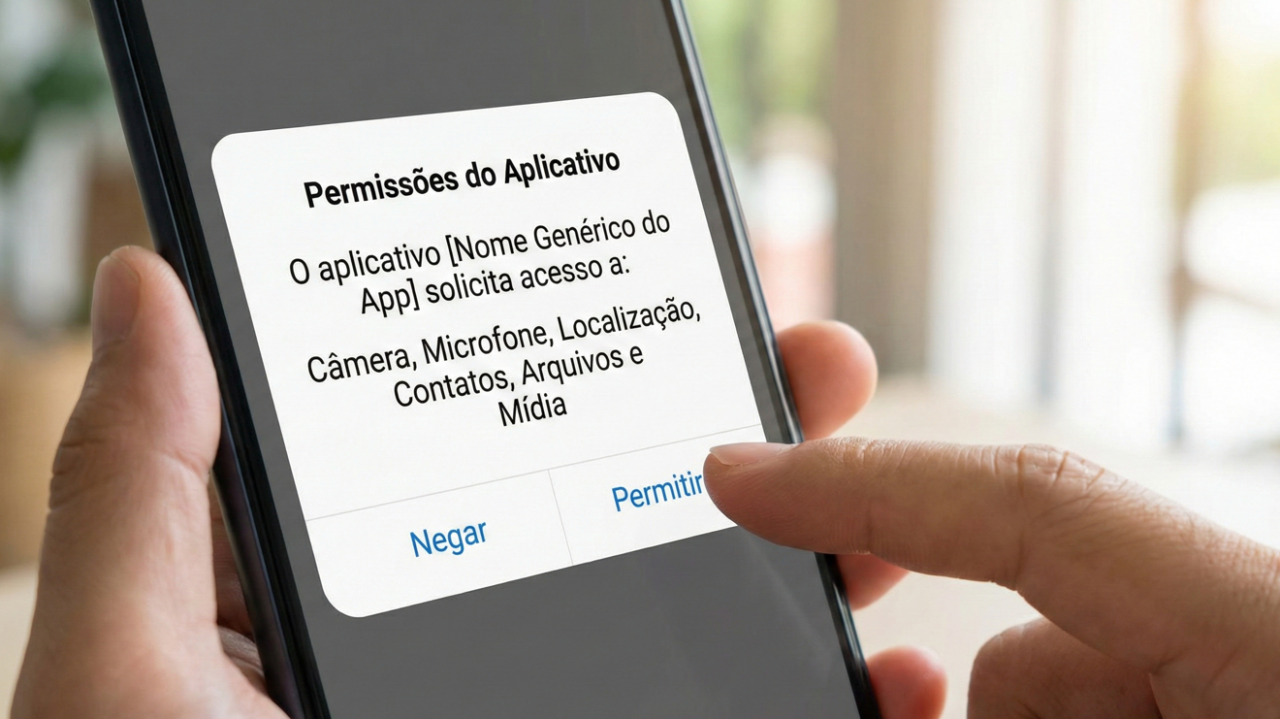
In practice, the issue appears in situations such as accessing location, microphone, camera, contacts, files, notifications and running in the background. These are common uses, but each requires a different combination of speed, quality, privacy and ease. The safest recommendation is to avoid choices based solely on ranking, advertising or isolated recommendations. What works for one routine may be excess for another. Therefore, HTechBD's editorial approach favors verifiable criteria: clarity of purpose, consistency, acceptable risk and simple maintenance.
First diagnosis
Permission must accompany function. A flashlight app doesn't need contacts; a photo editor may need images, but not necessarily a permanent location. When it comes to reviewing application permissions, it's worth transforming the evaluation into concrete questions: what needs to happen every day, who depends on the result, what data goes into the process and what would be the cost of a failure? This approach reduces impulse decisions and shows whether the chosen solution solves the entire task or just the most visible part of it.
The first step is to write the problem in a short sentence. For people who have installed many apps over time, this phrase avoids dispersion. Instead of looking for a 'full-featured' tool, look for a solution that handles the main scenario well: accessing location, microphone, camera, contacts, files, notifications, and running in the background. Then, look for hidden dependencies like required account, unstable sync, broad permissions, or disproportionate learning curve. The real usefulness often appears in the less flashy details.
Adjustments that make a difference
The review should look at continuous access, not just the moment of installation. Old apps accumulate forgotten permissions. When it comes to reviewing application permissions, it's worth transforming the evaluation into concrete questions: what needs to happen every day, who depends on the result, what data goes into the process and what would be the cost of a failure? This approach reduces impulse decisions and shows whether the chosen solution solves the entire task or just the most visible part of it.
Practical criteria
A good test lasts a few days and uses real cases, not perfect examples. If the solution only looks good when everything is organized, it may not support the routine. Test with incomplete file, bad connection, rush, interruptions and need to go back. When reviewing application permissions, the ability to fix errors, export data and explain what happened weighs as much as the list of features published on the home page.
How to create a simple rule
When there is an option, prefer to grant access only during use or to selected files. When it comes to reviewing application permissions, it's worth transforming the evaluation into concrete questions: what needs to happen every day, who depends on the result, what data goes into the process and what would be the cost of a failure? This approach reduces impulse decisions and shows whether the chosen solution solves the entire task or just the most visible part of it.
Another point is to define limits. Not everything needs to be automated, installed, purchased or configured. Often, a clear manual procedure is better than a poorly maintained complex tool. Use technology where there is repetition, risk of forgetting or need for standardization. Keep sensitive decisions under human review, especially when they involve personal data, money, reputation or communication with others.
Periodic review
Permission must accompany function. A flashlight app doesn't need contacts; a photo editor may need images, but not necessarily a permanent location. When it comes to reviewing application permissions, it's worth transforming the evaluation into concrete questions: what needs to happen every day, who depends on the result, what data goes into the process and what would be the cost of a failure? This approach reduces impulse decisions and shows whether the chosen solution solves the entire task or just the most visible part of it.
Warning sign
Warning signs often appear early: absolute promises, lack of documentation, difficulty canceling, excessive permissions, vague language about privacy, or dependence on a single vendor. This does not mean rejecting all new things. It means creating a pause before handing over important data, time or processes to something that has not yet demonstrated sufficient stability for its use.
Expected result
The review should look at continuous access, not just the moment of installation. Old apps accumulate forgotten permissions. When it comes to reviewing application permissions, it's worth transforming the evaluation into concrete questions: what needs to happen every day, who depends on the result, what data goes into the process and what would be the cost of a failure? This approach reduces impulse decisions and shows whether the chosen solution solves the entire task or just the most visible part of it.
To maintain the result, create a simple review. Ask monthly if the tool continues to solve the problem, if there are duplicate steps and if someone has become dependent on a process that no one understands. When reviewing application permissions, light maintenance is part of the solution. Without it, even the most promising technology becomes a digital drawer full of forgotten settings.
Quick checklist before deciding
- Define the main problem before choosing the tool.
- Test with a real case linked to access to location, microphone, camera, contacts, files, notifications and running in the background.
- Check privacy, permissions, export and support.
- Compare the time saved with the maintenance effort.
- Review the decision after a few days of use, not just upon installation.
This checklist seems simple, but it avoids a common pitfall: confusing a feeling of progress with concrete improvement. For people who have installed many apps over time, the best indicator is to see less rework, less doubt and more predictability. If technology requires constant explanations, creates unnecessary dependence or forces the user to change their entire routine without proportional benefit, it deserves to be rethought. Mature adoption is incremental and reversible.
The most consistent path is to combine curiosity with prudence. reviewing application permissions can bring clear gains, but only when there is purpose, review and limit. Before adopting any solution as a rule, observe whether it saves time, improves quality or reduces risk. If it doesn't deliver at least one of these results, perhaps it's just another layer of digital complexity.